Electronic mail fraud is a giant drawback for manufacturers, companies, and
customers alike. Spammers, spoofers, and scammers who sneak their method into an
inbox could cause a variety of injury. However sensible, accountable e-mail entrepreneurs can
take steps to forestall disasters.
That’s the place e-mail authentication protocols come to the
rescue and supply a way of safety for each senders and recipients.
If somebody offers you permission to achieve them by way of e-mail,
you’re getting into a relationship that ought to be constructed on belief and respect. When
a subscriber sees an e-mail from you, they shouldn’t be afraid to open it. However
there are many unsavory characters on the market who might attempt to impersonate
your model utilizing phishing emails.
Entry to somebody’s e-mail inbox is energy and as Spider-Man
is aware of very properly:
“With nice energy comes nice accountability.”
~ Uncle Ben Parker
And even Spider-Man offers with imposters who attempt to
impersonate his web-slinging methods.

Leap to a piece on this information:
Electronic mail authentication protocols are unsung heroes working behind the scenes to confirm that senders are who they declare to be earlier than emails attain inboxes. Implementing these verification strategies not solely reveals accountability but in addition improves e-mail deliverability.
The protocols can get fairly technical, and all of the acronyms
would possibly remind you of a bowl of Alpha-Bits cereal. However let’s begin by exploring
the fundamentals.
What’s e-mail authentication?
Electronic mail authentication is the method of utilizing a number of
strategies to make sure that messages will not be faked or solid earlier than they get
delivered. Mail servers on the receiving finish use e-mail authentication protocols
to confirm the sender title within the “from” area and different info positioned in
the e-mail header.
These protocols additionally test to verify emails weren’t
altered in transit, and so they inform mail servers what to do with messages that
aren’t authenticated.
Electronic mail authentication protocols shield us from spam and
phishing makes an attempt, particularly a kind of phishing often known as e-mail spoofing.
What’s e-mail spoofing?
Electronic mail spoofing includes messages that seem like from a identified or dependable sender, however they’re really an try to accumulate delicate knowledge corresponding to entry to an individual’s funds or on-line accounts. Electronic mail spoofing results in a faux web site with a bogus login web page the place targets are requested to enter credentials or different info.
These e-mail phishing makes an attempt usually attempt to forge the sender
title in addition to imitate the look of emails from recognizable manufacturers together with
monetary establishments, social media websites, or on-line retailers like
Amazon.com.
Amazon
spoofing is so widespread the corporate has its personal e-mail deal with for reporting
potential scams and suspicious communications.
Instance of an Amazon e-mail spoof

Even savvy web customers will be tricked with e-mail
spoofing. Intelligent scammers usually prey on the worry of getting hacked to trick
individuals. That’s why e-mail authentication protocols are so useful. They maintain
malicious messages from ever reaching the inbox.
How does e-mail authentication work?
Electronic mail authentication includes a number of attainable strategies of
validating the origin of an e-mail and area possession of message switch
brokers (MTAs) that had been concerned in transferring or modifying an e-mail.
Put merely, emails are despatched from a sure area or
subdomain. Electronic mail authentication protocols are guidelines positioned in DNS (area title
system) data for these sending domains. To authenticate an e-mail, the
sending mail server and receiving mail server speak to one another, double-checking
protocols within the DNS for affirmation.
Whereas every protocol is exclusive, it usually works like
this:
- The sender/area proprietor establishes guidelines for authenticating emails despatched from or on behalf of its domains.
- The sender configures sending e-mail servers and publishes the principles within the DNS data.
- Mail servers that obtain emails authenticate messages from the sender utilizing the revealed guidelines.
- Receiving e-mail servers then observe the revealed guidelines and both ship, quarantine, or reject the message.
Along with verifying legit senders, e-mail authentication
protocols additionally assist set up IP deal with and area fame in order that
malicious senders will be extra simply recognized.
The 4 e-mail authentication protocols
Easy Mail Switch Protocol (SMTP) is the usual basis upon which e-mail is constructed. It’s what’s used to ship and obtain messages. Nonetheless, SMTP doesn’t embody a method to validate a sender’s id, which is what makes it prone to spammers and phishing.
Electronic mail authentication protocols emerged within the early 2000s as a method to improve the safety of SMTP and thwart the rise of e-mail spam. SPF and DKIM had been the primary extensively adopted strategies. DMARC quickly adopted as a coverage to verify and lengthen SPF and DKIM.
BIMI is the brand new child on the block.

BIMI leads to a method for recipients to visually confirm the authenticity of an e-mail with a emblem displayed within the inbox. It additionally helps higher branding and serves because the payoff for having a strong e-mail authentication coverage.
These 4 e-mail authentication protocols present a
standardized method for e-mail purchasers corresponding to Gmail, Outlook, and Apple Mail to
confirm the id of senders versus utilizing separate, proprietary
strategies to authenticate e-mail.
So, whereas e-mail authentication may appear sophisticated,
technical, and even a bit messy … these protocols do present some
standardization. Electronic mail entrepreneurs ought to be glad we don’t need to observe
totally different protocols for each mailbox supplier.
Let’s take a better take a look at SPF, DKIM, DMARC, and BIMI.
1. SPF (Sender Coverage Framework)
The Sender Coverage Framework, or SPF, is an e-mail authentication
protocol that gives a DNS report specifying which IP addresses or hostnames
are approved to ship e-mail from a website.
SPF is a DNS TXT entry that allows the receiving mail server to test that an e-mail claiming to return from a sure area is related to a licensed IP deal with. The receiving server does this by wanting up guidelines for the bounce or return-path area within the DNS report. That’s in comparison with the principles within the SPF report to make sure there’s a match.
With out implementing SPF, mailbox suppliers are more likely to mark messages as spam.

In some instances, e-mail service suppliers (ESPs) deal with SPF
implementation robotically. That’s as a result of the ESP might present the IP deal with
and the return path. Nonetheless, for those who ship a excessive quantity of e-mail, you possible
need to keep away from utilizing a shared IP deal with. A devoted IP helps you management
sender fame. Understand that if you’re on a shared IP deal with, your
SPF report might should be up to date whenever you change ESPs.
One of many downsides of SPF is that it received’t work when
emails are forwarded. In case your model is one which depends closely on e-mail
word-of-mouth (getting your viewers to ahead your message), there’s a good
likelihood of the SPF failing validation and by no means reaching anybody past your
record.
2. DKIM (DomainKeys Recognized Mail)
The subsequent e-mail authentication protocol is the results of two
strategies developed to forestall e-mail forgery. In 2004, Yahoo merged its
“DomainKeys” with Cisco’s “Recognized Web Mail.”
DomainKeys Recognized Mail,
or DKIM, makes use of an encrypted key often known as a digital signature. This signature is
added to e-mail headers to assist confirm a sender and affiliate a message with a
particular area. DKIM additionally must be arrange inside a sender’s DNS report.
You’ll be able to consider DKIM like a watermark or fingerprint that
is exclusive to an e-mail sender. In contrast to SPF, DKIM signatures proceed working when
an e-mail is forwarded.
There are literally two keys that make DKIM work. Directors
generate a public key on the DNS report in addition to a non-public key that mail
servers transporting the e-mail to the recipient use to confirm authenticity. The
personal key’s the DKIM signature within the e-mail header.
The digital signature lets the MTA or receiving mail server know the place info on the general public key will be retrieved for authentication of the e-mail. Lastly, the general public key’s used to confirm the encrypted key within the DKIM signature. This reveals a connection between the e-mail and the sending area the place the general public key’s positioned.

As safe as all of this sounds, it’s nonetheless attainable for hackers to come up with DKIM keys and use them to impersonate a sender. For that cause, it’s really helpful that DKIM keys are modified a couple of instances per 12 months.
In line with a 2015
article on CircleID.com, some ESPs might share DKIM signatures amongst
clients. That’s no good as a result of a compromised digital signature might affect
a bunch of firms directly. Hopefully, this challenge is not as widespread
because the article states. However, in case your ESP is offering your DKIM signature, it’s
a query that’s value asking.
If it’s worthwhile to produce your individual digital signature, there are
DKIM mills that assist create these e-mail authentication data for you.
You can too study extra
about DKIM signatures and see an instance report right here on our weblog.
3. DMARC (Area-based Message Authentication, Reporting, and Conformance)
It was really PayPal that led a gaggle in growing DMARC
know-how to enhance upon present e-mail authentication strategies. PayPal was
(and is) generally impersonated by cybercriminals utilizing faux emails. A number of
different massive manufacturers in addition to main mailbox suppliers instantly adopted the
technique.
Technically, DMARC isn’t an e-mail authentication protocol so
a lot as a coverage that mail servers on the receiving finish check with earlier than
delivering an e-mail. DMARC helps decide learn how to deal with a message when it
fails authentication.
This coverage, also called Area-based
Message Authentication, Reporting, and Conformance, is one more report
that’s revealed within the DNS. It specifies whether or not a sending area is utilizing
SPF, DKIM, or each protocols for authentication. DMARC is usually described as a
method to get one of the best out of SPF and DKIM as a result of it creates a standard framework
utilizing each protocols
For many individuals, lacking an vital, official e-mail is
even worse than letting spam get via to their inbox. Actual emails can
typically fail DKIM and SPF authentication for numerous causes. So, mailbox
suppliers might let emails via in the event that they don’t move the check however seem to return
from a legit sending area. DMARC makes it extra clear what to do.
A DMARC coverage permits senders to create a framework that defines its e-mail authentication strategies and dictates learn how to deal with messages that violate the coverage. There are three choices area homeowners can select to specify the therapy of emails that fail DMARC validation:
The three DMARC p= insurance policies:
- p=none: Take no motion. Deal with the e-mail
as if there have been no DMARC validation. This coverage additionally helps acquire an
understanding of the e-mail stream with out impacting circulation. - p=quarantine: Settle for the e-mail however ship
it to a junk or spam folder as an alternative of the primary inbox. Or, isolate the
suspicious message for additional inspection. - p=reject: Cease supply of the e-mail to
any folder. The sender might be knowledgeable why the e-mail is just not getting delivered.
A DMARC coverage that rejects unvalidated emails is the strongest, however it may possibly imply e-mail from a website stops flowing if for some cause SPF and DKIM are failing.
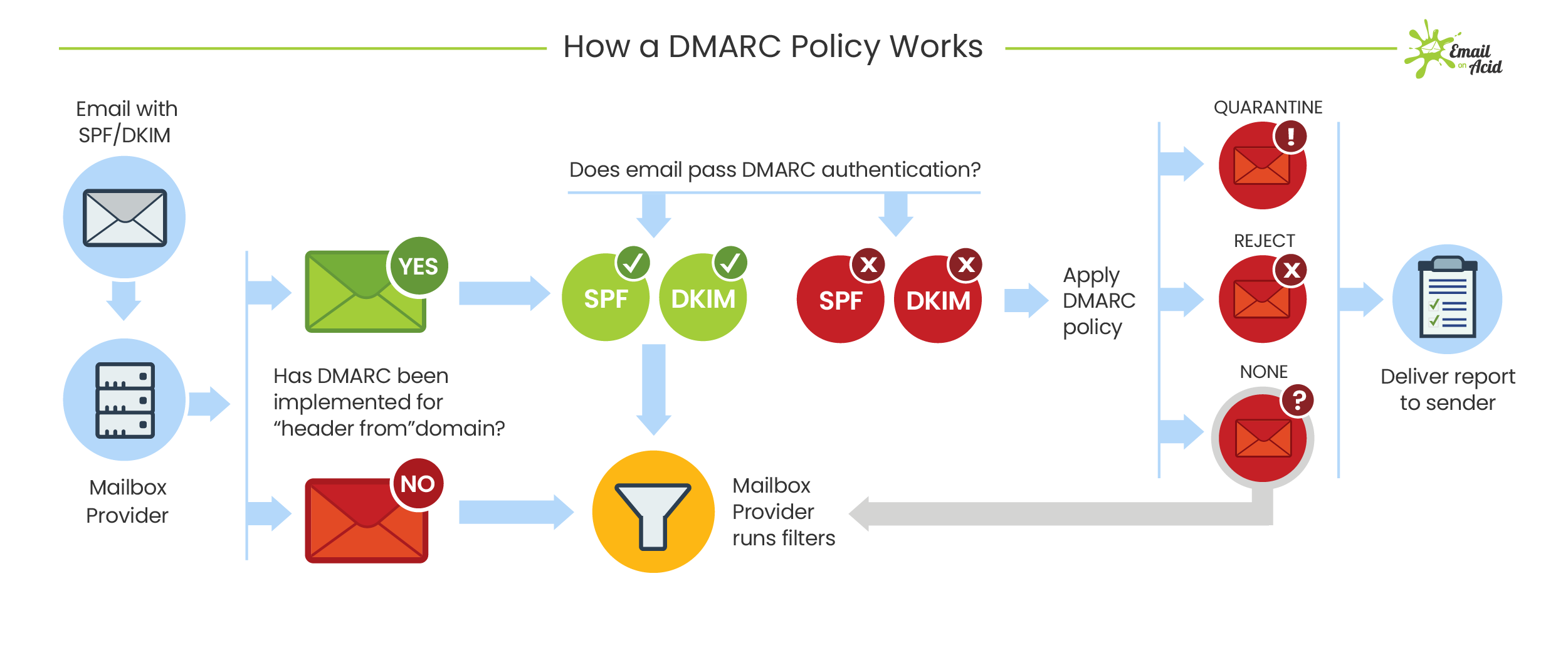
A advantage of implementing a DMARC coverage is that senders get
common DMARC experiences, which give the next info:
- Which servers and third events are sending mail
to your specified area. - The share of emails that move DMARC.
- What servers or third events are sending emails
that failed DMARC. - What actions receiving mail servers tackle
unauthenticated emails.
DMARC nonetheless isn’t good. Like SPF, it may possibly break throughout e-mail forwarding. DMARC may be troublesome for senders to arrange, and issues over stopping the circulation of official emails discourage stringent insurance policies.
Nonetheless, in case your group manages to arrange and
implement a profitable DMARC coverage, you’ll have an efficient method to cease most phishing
emails that try to spoof your sending area.
4. BIMI (Model Indicators for Message Identification)
BIMI is the most recent e-mail authentication protocol. In contrast to the
different specs, BIMI leads to one thing your subscribers can see in
their inbox. When applied accurately, BIMI shows a brand-designated emblem
subsequent to messages within the inbox.
The BIMI emblem reveals an e-mail will be trusted as a result of it means different e-mail authentication strategies are in place. It supplies subscribers with a sign that an e-mail is certainly genuine. This provides an extra stage of safety as a result of, even when scammers handle to get a phishing e-mail delivered, it received’t show a emblem.

In an effort to get mailbox suppliers to show a BIMI emblem,
you could have a completely functioning DMARC coverage in place with SPF and DKIM
data arrange. In some methods, BIMI is the payoff for pursuing the opposite e-mail
authentication strategies.
Like the opposite protocols, BIMI is a TXT report tied to a
area’s DNS. However, earlier than you set a BIMI report in place, it’s worthwhile to have a correctly
formatted emblem.
Appropriate BIMI logos are SVG recordsdata within the form of a
good sq., which will be cropped right into a circle. They require a strong
background and ought to be revealed by way of HTTPS. BIMI emblem recordsdata should be small
and shouldn’t exceed 32kb. Lastly, your emblem should even be a registered
trademark to fulfill requirements.
Adoption of BIMI for e-mail authentication is ongoing. So
far, a restricted variety of mailbox suppliers assist the show of BIMI logos.
That features Yahoo, the Australian e-mail shopper Fastmail, and Verizon providers
corresponding to AOL and Netscape.
Google launched a Gmail pilot program for BIMI in 2020. In July of 2021, information broke that Gmail is formally rolling out full assist for BIMI. That’s massive information as a result of it’s possible {that a} sizeable portion of your record is utilizing Gmail. It definitely makes the effort and time of establishing e-mail authentication protocols appear much more worthwhile.
Implementing BIMI ought to finally improve subscriber confidence within the supply of your emails. Get extra recommendation, assets, and instruments at BIMIGroup.org. You can too hear from two BIMI Group specialists in our AMA on Model Indicators for Message Identification.
Get extra BIMI steering [free download]

Obtain our free report on BIMI. Get insights from specialists and tips about learn how to get your model’s emblem to show in e-mail inboxes.
Must you use all 4 e-mail authentication protocols?
You know the way they are saying, “two heads are higher than one”? That’s like utilizing each SPF and DKIM. You know the way Faculty Home Rock and Blind Melon say, “three is the magic quantity”? That’s like including BIMI to the e-mail authentication combine.
And as talked about, you’ll want DMARC to get essentially the most out of each these protocols and to get a BIMI emblem to show.
Whereas it might definitely take effort and time, establishing
sturdy e-mail authentication strategies is value it, particularly when you have the
assets.
The excellent news is — entrepreneurs shouldn’t need to deal with
e-mail authentication alone. You’ll most certainly must get your IT group or
cybersecurity specialists that can assist you set issues up in DNS data. Your ESP might
additionally must get entangled. Colleagues, distributors, or safety consultants ought to
have the ability that can assist you troubleshoot points as you’re employed to verify that e-mail
authentication protocols are working accurately.
Who ought to take e-mail spoofing significantly?
Whether or not or not you prioritize e-mail authentication relies upon
on how vital safety is to your model — and extra importantly — your
clients.
For main on-line retailers, monetary establishments, client
tech firms, and others coping with delicate private and enterprise
info, e-mail spoofing generally is a massive drawback.
Microsoft often tops a quarterly report from Verify
Level, a cybersecurity agency that lists the manufacturers most frequently spoofed in
phishing makes an attempt. Different regulars on the phishing manufacturers record embody main
banks like Wells Fargo and Chase. PayPal and Dropbox usually make the record as do
social websites like LinkedIn, Instagram, and Fb. Electronic mail spoofing even targets
youngsters utilizing the net recreation Roblox.
Nonetheless, you don’t need to be a big firm to get
spoofed by scammers. An article from Kelly Sheridan on Darkish
Studying says criminals at the moment are utilizing smaller manufacturers for e-mail spoofing. The truth is, that consists of Verify Level,
the cybersecurity firm that publishes the model spoofing record. Sheridan
writes:
“Many [smaller companies] don’t have assets to detect fraudulent web sites; consequently, a spoofed website could possibly be up for days or perhaps weeks earlier than the model proprietor takes it down … It’s incentive for attackers to keep away from massive manufacturers with extra refined defenses.”
The Federal
Commerce Fee (FTC) has extra data on what to do if your small business is
spoofed.
The
advantages of e-mail authentication
In case you’re on the fence about e-mail authentication protocols,
otherwise you want a method to persuade others in your group that it’s value
implementing, listed here are the important thing benefits:
1. Defend your clients and subscribers
It will not be your direct accountability to cease e-mail
spoofing from fooling individuals, and it’s unlikely you’d be held answerable for a
buyer who will get scammed. Nonetheless, the truth that e-mail entrepreneurs can do
one thing means we must always.
Regardless that a phishing rip-off isn’t your fault, that will not
be how your clients understand it. Actually, clients who’re scammed by
e-mail spoofing of your model might develop into very hesitant to open and interact with
official emails from you. Which ends up in the subsequent profit …
2. Defend your model fame
In a world the place everybody faces cybersecurity threats every day, manufacturers which have a fame for being protected and safe are trusted.
Phishing emails exploit belief in your model. In case you can cease
these malicious messages from reaching inboxes, you’re additionally stopping the
erosion of belief. Electronic mail authentication protocols are instruments you should use to cease
phishing and shield your model’s fame.
Talking of fame, e-mail authentication additionally helps you
set up a robust sender fame. That leads us to learn quantity three …
3. Assist e-mail deliverability
Electronic mail authentication can have a direct affect on e-mail deliverability charges. When mailbox suppliers can affirm the supply of an e-mail and the id of the sender, it may be confidently delivered to inboxes.
Alternatively, failure to implement e-mail authentication protocols will increase the probability of official communications touchdown in spam or getting rejected by mailbox suppliers. Electronic mail authentication is without doubt one of the simplest methods entrepreneurs can management e-mail deliverability.

Involved about e-mail deliverability?
Take a look at our e-mail deliverability information! Study the ins and outs of learn how to keep out of spam folders be certain your campaigns make it into your subscribers’ inboxes.
Extra methods to handle deliverability
There are a selection of things that affect e-mail deliverability. The perfect e-mail entrepreneurs handle the points which might be inside their management, and so they monitor deliverability persistently.
Electronic mail on Acid’s deliverability options allow you to double-check and validate campaigns earlier than hitting ship. Verify to see in case your area is on a blocklist and discover out in case your messages move or fail assessments for greater than 20 totally different spam filters.
Electronic mail deliverability apps and providers from Pathwire make sure you’re solely accepting legitimate e-mail addresses and assist predict potential points. Plus, Pathwire’s e-mail deliverability specialists help manufacturers in creating tailor-made options and an in depth technique for inbox placement.
Prioritizing and investing in e-mail deliverability is crucial if you wish to maximize your model’s funding in e-mail advertising and marketing.
Enhance Deliverability to Hit Extra Inboxes!
Nothing ruins a elegant e-mail’s ROI potential like a visit to the spam folder. Run a Spam Check proper inside your Marketing campaign Precheck workflow so you’ll be able to land in additional inboxes and improve e-mail ROI. With Electronic mail on Acid, you’ll be able to test your e-mail towards 23 of the preferred spam filters and your area towards the preferred blocklists earlier than you hit “ship”. Join a free trial and take a look at it out at the moment.

Creator: Betsy Grondy
With a decade of e-mail advertising and marketing expertise, Betsy has achieved e-mail technique and execution for greater than 36 international locations (for native manufacturers in addition to Fortune 500 firms) all from the consolation of her North Carolina dwelling. As Electronic mail on Acid’s Senior Electronic mail Advertising and marketing Supervisor, she’s having fun with being meta in e-mail advertising and marketing and striving for e-mail perfection in each ship. When she’s not pushing the boundaries as an #emailgeek, you’ll discover her scouring flea markets together with her husband for cool classic toys and mid-century trendy furnishings to revive.
Creator: Betsy Grondy
With a decade of e-mail advertising and marketing expertise, Betsy has achieved e-mail technique and execution for greater than 36 international locations (for native manufacturers in addition to Fortune 500 firms) all from the consolation of her North Carolina dwelling. As Electronic mail on Acid’s Senior Electronic mail Advertising and marketing Supervisor, she’s having fun with being meta in e-mail advertising and marketing and striving for e-mail perfection in each ship. When she’s not pushing the boundaries as an #emailgeek, you’ll discover her scouring flea markets together with her husband for cool classic toys and mid-century trendy furnishings to revive.